The TLS 1.3 Countdown Is On and It’s Time to Get Ready
Updated September 25, 2021.
It is reported that cybersecurity attacks are up 300 percent during the COVID-19 pandemic. In this blog, I highlighted the risks associated with working remotely, and possible options to address them. One element I briefly touched on is the importance of decrypting traffic. This blog covered the basics of SSL, TLS and HTTPs. Here I’ll elaborate more on TLS 1.2, the need to move to TLS 1.3 and what to look for in an inline decryption solution.
It is estimated that about 90 percent of enterprise web traffic is encrypted using some version of SSL/TLS. TLS (Transport Layer Security) is a tunneling protocol that encapsulates application payload like DNS, HTTP, FTP, SIP, SMTP and others. TLS session establishment has two phases — the first is asymmetric encryption and the second is symmetric. The first phase is between the client and server to agree on the protocol version (TLS 1.1, 1.2, 1.3) cryptographic algorithms, cipher suites, and exchange and validate digital certificates to establish trust. Additionally, shared key exchange is generated to be used in the second symmetric encryption phase to exchange payload.
Why Decryption Is Critical
Attackers are now using encryption to transport malicious traffic applications exploits into and out of the enterprise environment, and encrypting the threat. According to Gartner, about 50 percent of malware attacks are encrypted. And in 2020, about 60 percent of organizations are failing to effectively decrypt this traffic. This huge gap leaves enterprises extremely vulnerable to attacks and exploitations.
Where Do You Apply Decryption?
In any data center there is both North-South and East-West traffic. The North-South traffic can be inbound, where external users are coming to your data center (DMZ). The other scenario is where your internal users are going out, accessing content on the web. The majority of the traffic in the data center is East-West. This is the communication between internal users and applications, as well as between applications.
Typically, there are two decryption considerations: passive out-of-band and active inline (i.e. man-in-the-middle). Out-of-band is not applicable when using ephemeral or perfect forward secrecy (PFS) encryption (which TLS 1.3 enforces with restricted cipher suites support), and is limited to inbound deployments where private keys are available; inline man-in-the-middle decryption is required to decrypt PFS-based cipher suites and TLS 1.3. Inline man-in-the-middle decryption can be applied to support all scenario modes for North-South and East-West traffic inspection.
TLS 1.3 Closes the Security and Performance Gaps of TLS 1.2
However, this creates challenges to enterprise networks as it hides valuable metadata, blinding current security monitoring tools to the content so they are unable to detect threats. Furthermore, passive decryption is not possible due to the use of ephemeral key decryption available only during that’s unique for each session.
Today, the majority of web traffic uses TLS 1.2, which was the most current version of TLS until TLS 1.3 was introduced in August 2018. TLS 1.3 adoption rate is on the rise as more web services and enterprise networks embrace the technology (the four top web browsers support TLS 1.3 by default).
In TLS 1.2, both the server name in the client hello communication and the certificate from the server response are visible. In TLS 1.3, the server name extension in the client hello communication can be encrypted, and the certificate from the server response is encrypted.
According to the Forrester report “Maintain Security Visibility in the TLS 1.3 Era, July 2020,” “you have two years to prepare your security tools for TLS 1.2 and DNS-over-HTTPS.” To protect your network and organization, it’s critical to start acting now and prepare for the widespread adoption of TLS 1.3 and DNS over HTTPs.
Do It Well, Do It Once
That’s the recommendation from the NSA cybersecurity information report when decrypting and encrypting in enterprise networks. In order to minimize risks in breaking and inspecting TLS traffic, inspection should only be conducted once within the enterprise network. Redundant TLS inspection, wherein a client-server traffic flow is decrypted, inspected and re-encrypted by one forward proxy, and then forwarded to a second forward proxy for more of the same, should not be performed. Inspecting multiple times can greatly complicate diagnosing network issues with TLS traffic. Further, it obscures certificates when trying to ascertain whether a server should be trusted and adds unwanted latency to the network.
What to Look for in an Inline SSL/TLS Decryption Solution
When choosing an inline decryption solution, there are several things to consider. In this infographic, a summary of each is listed.
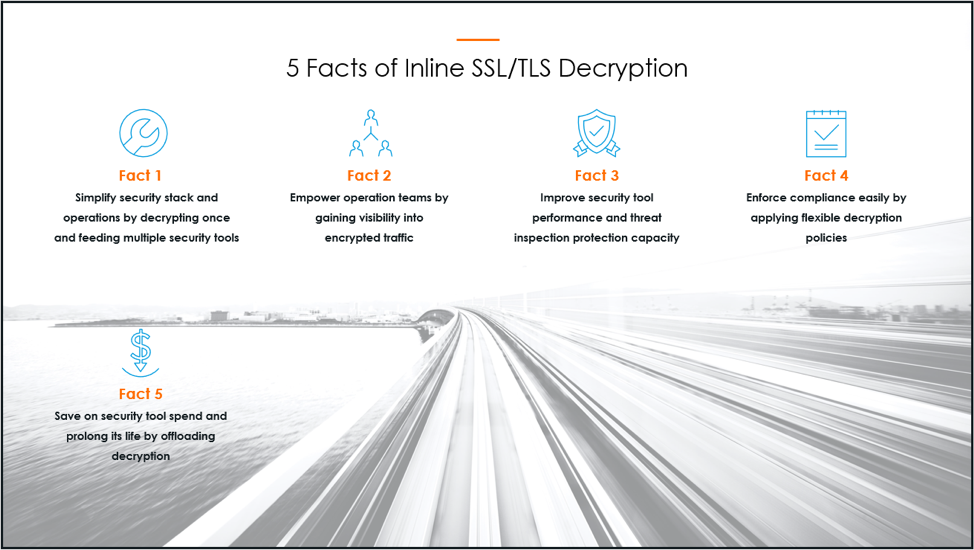
Fact 1: Decrypting once and feeding multiple security tools simplifies operations and the security stack. The InfoSec team doesn’t have to employ multiple devices for decrypting and encrypting that lead to complexity, difficulty in troubleshooting and increased latency.

Fact 2: By gaining complete visibility into encrypted traffic including TLS 1.3, InfoSec and NetOps teams, as well as security tools, are empowered with unparallel visibility to analyze and detect threats.
Fact 3: By offloading decryption from security tools and providing decrypted traffic, the performance of the tools is significantly enhanced to inspect threats without dropping packets as well as prolonging the life of the tools. Furthermore, latency is reduced by minimizing the number of times needing to decrypt and re-encrypt.
Fact 4: With the ability to apply flexible decryption policies based on traffic type, detect TLS on random ports to improve protection, apply masking to copies of traffic, plus being FIPS 140-2 Level 2 certified, organizations are easily able to adhere to regulations and compliance requirements.
Fact 5: By offloading decryption from overburdened security tools, organizations are able to protect and extend current investment and spend less on purchasing new tools.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Security group.
Share your thoughts today