How Gigamon Helps Black Hat kNOCk Out Threats
Gigamon is honored to be selected as one of six vendors to help secure the 2021 Black Hat Conference network for the fourth year in a row. This blog post covers how Gigamon plays its part in building a secure environment for Black Hat NOC and helps to knock out threats.
The Black Hat Conference has become the epitome of security conferences worldwide. The conference, sponsored by Informa Tech (formerly UBM), takes place under the Black Hat Umbrella and is held three times a year in the U.S., U.K., and Singapore. Security experts, students, professionals, and hackers from all over the world gather at the conference to attend briefings and trainings addressing growing security needs.
Black Hat NOC has one of the most diverse and state-of-the-art technologies deployed in a very short time frame to provide network and security for all events at the conference, including trainings, briefings, and everything else happening at the conference. NOC leaders Neil Wyler (@grifter801) and Bart Stump (@thestump3r) have hand-picked best-in-class vendors to be part of Black Hat NOC, namely RSA Security, Palo Alto Networks, Ruckus Networks, CenturyLink, Gigamon, and Cisco.
Tap and agg and much more: One of the key requirements for building any secure environment is ensuring that all traffic from every corner and blind spot of the network is captured. While this can be done using SPAN ports, it has been proven time and again that a network packet broker is best suited for this job. Gigamon sits between the network and security stack for Black Hat NOC, ensuring all traffic is passing through Gigamon and providing that traffic to the desired security tool (RSA) seamlessly. While Gigamon can provide this traffic flawlessly, it also helps remove duplicates and noise from the traffic at the same time. This ensures that security tools are performing at their best efficiency without seeing any irrelevant traffic.
Bypass protection: One of the major concerns during these events, and generally for any high-functioning network environment, is uptime or availability of the network. Since Gigamon sits inline with the security and network stacks, any glitch or issue on the security stack does not cross over to the network stack, meaning Gigamon has the ability to bypass any security tool if for some reason that tool stops passing traffic. Built-in heartbeat protection keeps a check on the health of security tools and ensures the network is never impacted by any issues from the security tools side. While such a scenario has never happened in the time Gigamon has been part of the Black Hat NOC, this provides peace of mind in knowing that network operations won’t be impacted.
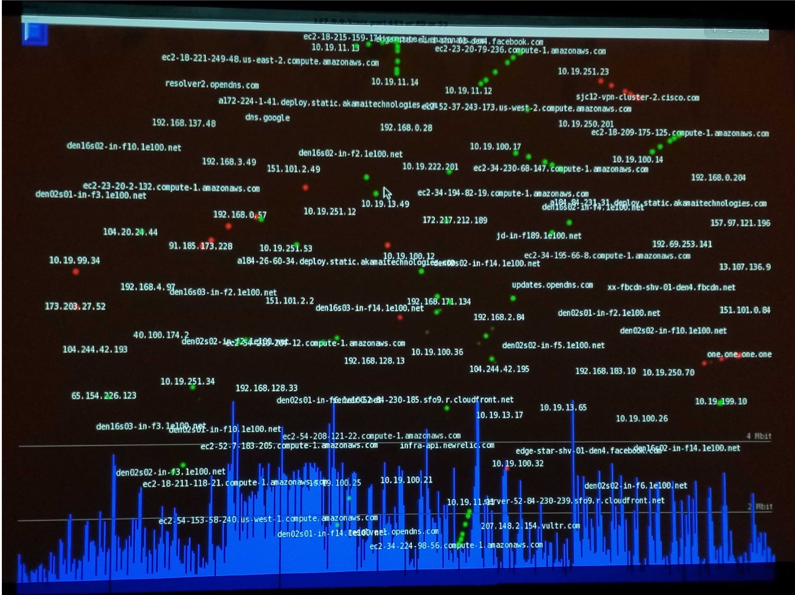
Slice it up: Black Hat NOC team has built a very cool-looking tool which runs on Intel NUCs and serves like a watchtower for NOC. Although this tool is very efficient in showing an overall picture of the network with different hosts communications, because it’s running on Intel NUC hardware, it cannot keep up with the amount of traffic coming into its 1G port. This is where Gigamon steps in and helps and make this tool more efficient. Since this tool requires only the header information, Gigamon efficiently slices the packet up and provides exactly what the tool needs to see. This has improved the tool efficiency 90 percent by sending it more traffic than it could previously handle.
Load balancing: Sitting between the network stack and security stack provides one great benefit for environments: segregating the need for security tools dependency on network speed. Although network and security tool vendors keep up with growing needs for network speed, this comes at a cost. Gigamon, being in middle of this stack, alleviates the need by aggregating the entire network stack at any speed, then delivering with the best speed fit to the security stack, improving efficiency and increasing cost savings. Although this isn’t needed for Black Hat NOC, since the amount of traffic never exceeds set parameters, if any such needs were to arise, the environment is ready to handle them with the help of Gigamon. The ability to load balance traffic helps security tools see traffic evenly and never get overwhelmed — and if any tool fails, the traffic will move over to another tool seamlessly.
Overall, Black Hat NOC is a fast-paced setup that ensures all the network and security operations are running smoothly. All the participating vendors provide best-in-class service to make this happen. Black Hat NOC is a true showcase of different vendors’ interoperability and goodwill for the cybersecurity community.
Featured Webinars
Hear from our experts on the latest trends and best practices to optimize your network visibility and analysis.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Security group.
Share your thoughts today