Public Cloud Traffic Visibility Made Simple with Gigamon, Part 2
In Part 1 of this series, you learned that visibility into cloud network traffic is a real sticking point for public cloud adoption. Only AWS offers a native visibility solution, its VPC mirroring service, but it does not meet all visibility needs and leaves you vulnerable to vendor lock-in. And installing tool agents in the cloud eats up metered cloud resources, increases management complexity, and can stumble in multi-cloud environments.
Fortunately, the Gigamon Visibility and Analytics Fabric™ is the answer to all these challenges. It helps you acquire traffic from all workloads, optimize traffic flow in the cloud to reduce tool load and network charges, and deliver traffic to the tools that need them, wherever those are.
Working in Tandem with Native Cloud Tools
The Gigamon Visibility and Analytics Fabric works with any native cloud visibility service to obtain a copy of traffic from monitored cloud workloads. For example, you can acquire copies of traffic from AWS’s VPC mirroring service, then send only the traffic of interest to your tools, which is not currently possible using native AWS mirroring service alone.
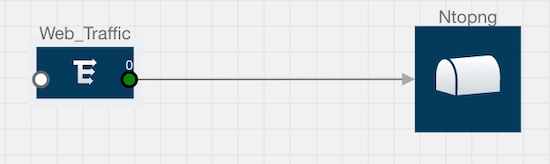
In this way, you can optimize tool resources and, in the process, save costs by only sending the traffic that is most important to the tools. For example, if a tool needs to see only web traffic, you can acquire and aggregate web traffic from all monitored workloads and then, using a highly intuitive drag-and-drop canvas, send the traffic to a desired on-premises or cloud-based tool destination, as shown in Figure 1.
Tool Optimization Through GigaSMART Operations in the Cloud
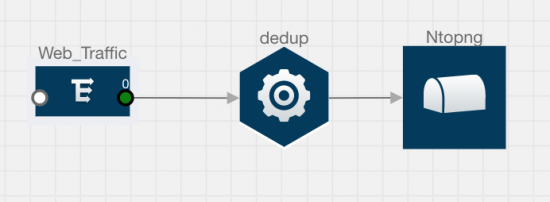
The Visibility and Analytics Fabric™ provides tool optimization using smart intelligence on your cloud traffic. You can use sampling, de-duplication, header stripping, NetFlow and masking to further winnow traffic down so it’s of laser-focused interest to your tools. De-duplication removes duplicate packets, cutting at least 33 percent and sometimes as much as 50 percent of the load on those tools. You just need to add de-duplication functionality in the link leading up to the tool, as seen in Figures 2 and 3.
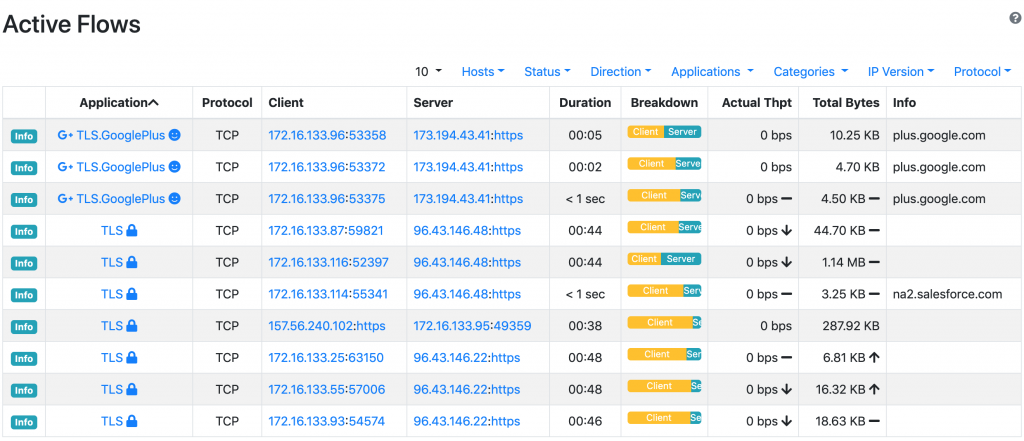
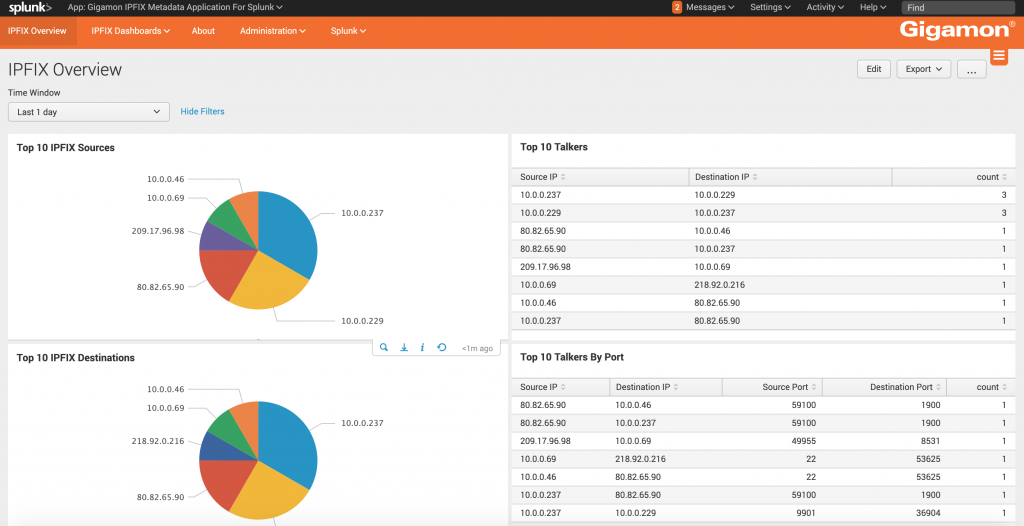
Similarly, you can generate NetFlow from raw traffic and send it to a SIEM like Splunk or QRadar as seen in Figures 4 and 5. This helps reduce the amount of traffic ingested by the SIEM, resulting in cost savings.
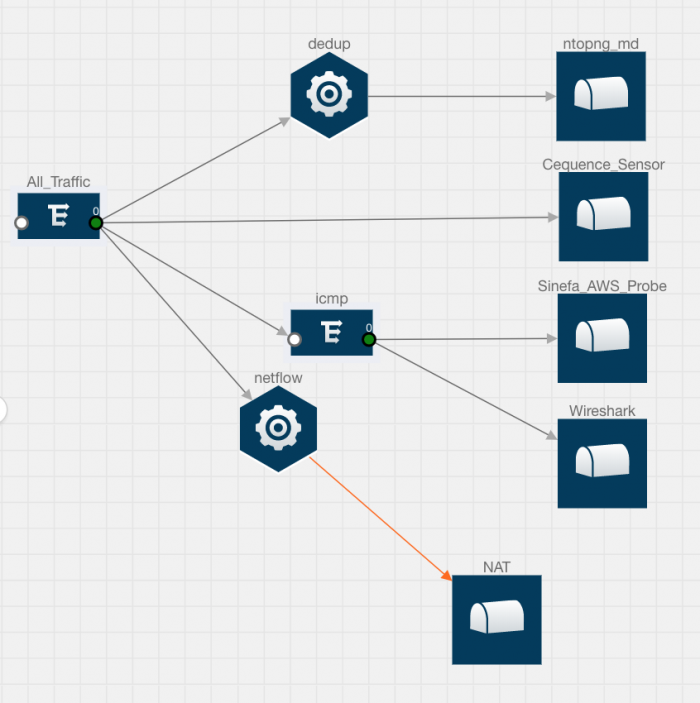
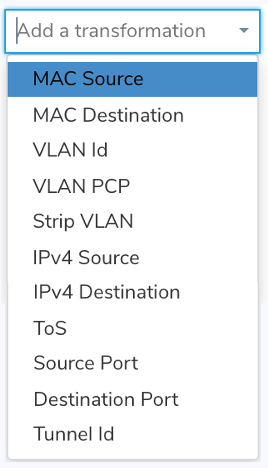
You can further transform packets for security and compliance reasons. For example, transformation gives you the ability to change source or destination IP, L4 ports, MAC, VLAN ID, or even change the tunnel ID (see Figure 6). Let’s say you have multiple links to the same tool instance. Because this tool or endpoint has multiple tools built in, you can transform tunnel IDs so that the tool can process packets at different tunnel destinations.
Acquire Traffic from All Workloads
Gigamon provides virtual TAPs that grab traffic from any cloud workloads running in any public cloud environment, such as AWS, Microsoft Azure and more. This overcomes the challenge faced if you need to acquire traffic from older EC2 instances not supported by the AWS VPC mirroring service — and, of course, if you’re using other public cloud environments, which lack native mirroring services. The traffic can then be optimized, as discussed above, before sending it to the tools.
Leverage the Visibility Fabric to Deliver Traffic to Your Tools
When you use the Visibility and Analytics Fabric for the cloud, you need only one Gigamon virtual agent to grab traffic from a workload, not multiple tool agents from different tool vendors. With this approach, your tools get the traffic they need to function, but the workloads you’re monitoring aren’t bogged down with multiple tool agents running on each and every workload.
Gigamon: A Savior for Agentless Tools
Agentless tools leverage the Visibility and Analytics Fabric by getting traffic from the Gigamon virtual TAPs. Customers can either send all of that traffic to the tools or optimize the traffic based on what the tools need. This helps cut down the time required to spin up new agentless tools.
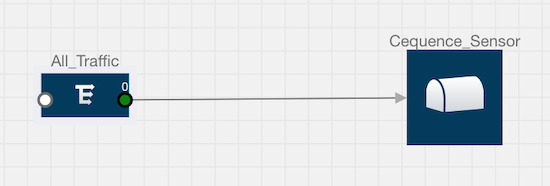
For example, a bot detection and mitigation security tool vendor named Cequence needed to acquire all cloud traffic from customers’ cloud workloads without deploying any agents. Cequence leveraged the Visibility and Analytics Fabric in the cloud instead of developing its own agent. As seen in Figures 7 and 8, within half a minute of connecting to a source of traffic, the Cequence sensor was showing all kinds of bot activities in the customer’s cloud environment.

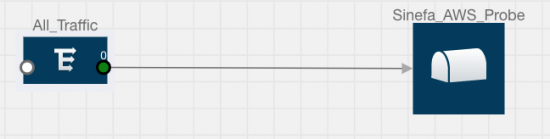
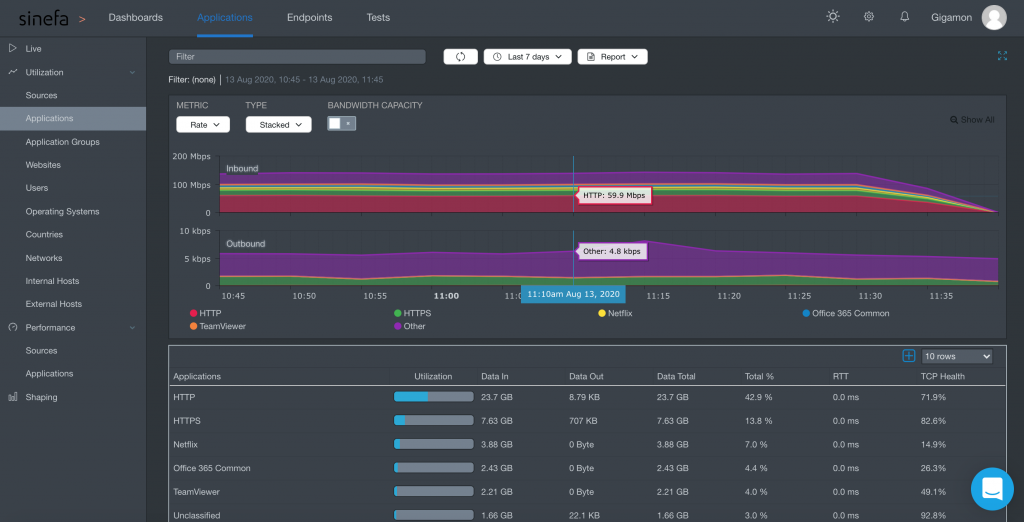
Similarly within no time, an APM tool from Sinefa also acquired all cloud traffic using Gigamon Visibility and Analytics Fabric for all monitored cloud workloads to measure user quality experience, as seen in Figures 9 and 10.
Multicloud Environment? No Problem!
The Visibility and Analytics Fabric enables you to acquire traffic from monitored workloads hosted in any public cloud environment and send mirrored traffic to any tool destination, regardless of the location of those tools. This means any tool — whether hosted on-premises, in AWS or Azure, or in any other public cloud — can receive traffic from any cloud workload.
Cloud vendors bill customers for any traffic leaving the public cloud network. GigaSMART® operations such as de-dup, NetFlow, masking and sampling can help reduce the amount of traffic leaving the cloud networks and heading for tools hosted either in other cloud environments or on-premises, resulting in a lower monthly bill.
No Matter Where Your Tools Are, Gigamon Will Bring Cloud Traffic of Interest to Them
Most IT organizations are heavily vested in security and performance measurement tools that are hosted on-premises. But at the same time, as part of their digital transformation, most enterprises are also spinning up new tools in public or private clouds. The Gigamon Visibility and Analytics Fabric provides great flexibility to acquire cloud traffic and distribute it to tools on-premises or in the cloud.
With it, you can send AWS traffic to a tool running in Azure, or send on-premises traffic to cloud-based tools running in any public cloud, or just send specific session traffic from the public cloud to a tool on-premises. No matter where you want to send traffic, Gigamon has you covered, offering the visibility you need to fully embrace cloud computing and the digital transformation.
Featured Webinars
Hear from our experts on the latest trends and best practices to optimize your network visibility and analysis.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Hybrid/Public Cloud group.
Share your thoughts today








