Gigamon ThreatINSIGHT Just Got Even Better
In May, we released ThreatINSIGHT™ 3.0, and since then, positive feedback has been rolling in. And now we’re excited to announce the release of ThreatINSIGHT 3.1 — so if you think 3.0 was special, what until you see what’s in the new version.
Here’s just some of the praise ThreatINSIGHT has received from customers and the press:
“A tool built for SecOps, not marketing campaigns,” declared one practitioner in Gartner Peer Insight Review. “Five stars all around for ‘Evaluation and Contracting,’ ‘Service and Support,’ ‘Integration and Deployment’ and ‘Product Capabilities,’” said another. And Gartner, Forrester and 451 Research have all listed ThreatINSIGHT as a “recognized vendor.”
You’d think positive buzz from customers and market analysts like that would go to our heads — but while we are flattered, we’re not resting on our laurels. After all, our mantra here at Gigamon is “Built by responders, for responders,” and we took all the feedback we’ve been hearing and created an even better solution.
What Is ThreatINSIGHT?
Gigamon ThreatINSIGHT is the first high-velocity cloud-native network detection and response (NDR) solution that enables you to detect, investigate and remediate threats — fast — in an ever-changing IT environment. Some highlights:
- Network visibility, threat detection and response
- Unequalled visibility
- High-fidelity threat detection
- Rapid, informed response
- Managed cloud-based SaaS solution
- Fully managed rapid deployments
- Constantly updated and managed detection engines
- Scalable and fast INSIGHT cloud data warehouse
- Always accessible web portal and APIs
- Teams spend time using ThreatINSIGHT, not managing it
- Backed by world-class expertise
- Detection engines (machine learning/behavioral/expert systems) and intelligence backed by Gigamon Applied Threat Research (ATR)
- Customers are supported by an assigned Customer Success member, all specialized former security analysts
What’s New with ThreatINSIGHT 3.1?
All NDR solutions worth their salt offer three critical capabilities:
- Visibility: Both breadth and depth of network traffic visibility
- Detection: The ability to identify hidden and emerging threats that preventative solutions missed
- Response: The ability to enable incident responders to quickly assess an incident and take mitigation actions
We’ve got great news: ThreatINSIGHT 3.1 bolsters capabilities across all three of those areas. Let’s take a look.
#1. Broader, Simpler Visibility into Your Cloud and Remote Workforce
Organizations that enabled virtual work have seen a huge jump in employees who access web applications and data without first accessing a VPN. That has created a much larger attack surface to monitor and defend. Additionally, many organizations have accelerated their digital transformation and moved workloads to AWS, creating even more vulnerabilities for threat actors to exploit.
To increase visibility for our customers, ThreatINSIGHT 3.1 now offers:
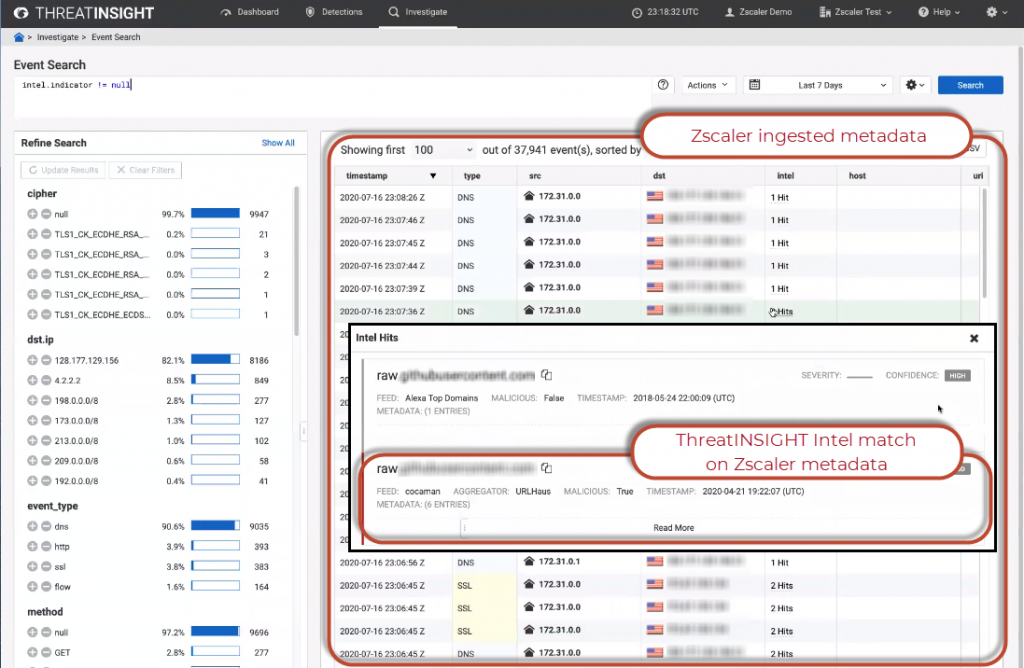
- Zscaler partnership and integration. By connecting directly to the internet through Zscaler, you can provide remote sites and teleworkers ThreatINSIGHT’s deep threat detection and response capabilities. Integration allows for simple deployment and connectivity to Zscaler through the ThreatINSIGHT portal.
- Gigamon Visibility and Analytics Fabric™ integration. Committed to unifying network operations and security operations teams, Gigamon has integrated ThreatINSIGHT into our Visibility and Analytics Fabric to eliminate blind spots and accelerate threat detection and response. Better together, Gigamon GigaVUE customers have the fastest and most effective mechanism to add network detection and response to their security stack. Deploying ThreatINSIGHT Sensors has never been easier with provisioning, management and troubleshooting delivered through the same GigaVUE-FM fabric manager interface that allows network operations teams to map and manage traffic flows, making blind spots a thing of the past. Security operations teams now have eyes across the entire attack surface and will benefit from ThreatINSIGHT’s accelerated, behavior-based threat detection and rapid, informed response workflows.
- Native AWS cloud sensors. Gain visibility into cloud workload traffic within AWS with native machine images that are easy to deploy and manage.
#2. Greater Lateral Movement and C2 Detection
ThreatINSIGHT provides high-fidelity, accelerated threat detection across the entire MITRE ATT&CK framework, and with ThreatINSIGHT 3.1 we continue to hone and expand our detection chops by offering:
- Lateral movement detections. Examine suspicious service creation behavior to identify malicious East-West movement of threat actors more quickly. Gigamon ATR created expert systems to run behavioral analysis detection on remote procedure call traffic (that is, the initiation of processes on a remote system) across the global dataset to identify malicious activity.
- C2 detections. Expand detection capabilities of elusive command-and-control activity. Gigamon ATR enhanced our supervised machine learning systems that run behavioral analysis of HTTP, DNS and SSL traffic across the global dataset to detect command-and-control activity for hidden and emerging threats.
#3. Faster Investigations and Integrated One-Click Mitigation Response
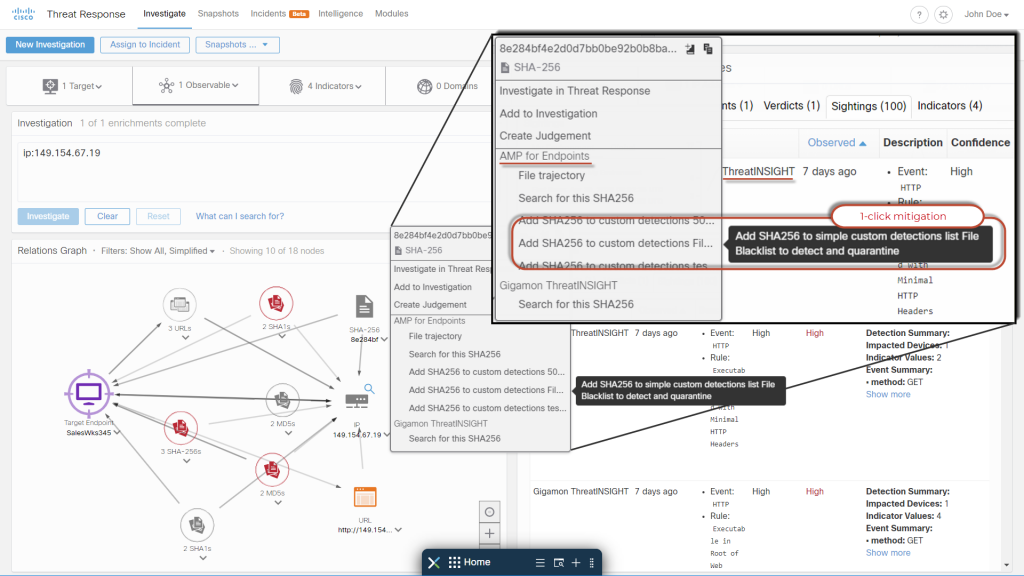
For incident responders, two things matter most: context and speed. ThreatINSIGHT 3.1 has added both, enabling responders to quickly access critical contextual data from within the ThreatINSIGHT Portal and respond through the Cisco SecureX platform integration.
- Cisco SecureX platform integration. Customers of both Cisco and ThreatINSIGHT gain unified visibility and data across all integrated Cisco and Cisco Partner solutions, including ThreatINSIGHT. Plus, they can take one-click mitigation actions through SecureX integrated network and endpoint solutions. Examples:
- Umbrella (DNS Firewall)
- Amp for Endpoints (EDR)
- Cisco Firewalls
- Cisco Email Security and Cisco Web Security
- UX enhancements. Speed up investigative efforts by adding UX enhancements, such as “Faceted Search,” customized dashboards and “Save and Share” IQL queries.
What Hasn’t Changed with ThreatINSIGHT 3.1
While we are continually improving ThreatINSIGHT, we also want to keep what’s working well. We know what works, and our engineering and ATR teams, with all their dedication to fueling innovation, aren’t going anywhere. We’ll also continue to assign each customer a Technical Account Manager, who is a trained, experienced incident responder and ThreatINSIGHT expert, to help customers ensure they get the most from our solution.
ThreatINSIGHT is more than software. With Gigamon ATR and our Technical Account Managers, you gain the team and tools required to combat cyberthreats. To learn more, visit the ThreatINSIGHT 3.1 webpage and request a specially prepared self-guided demo.
Featured Webinars
Hear from our experts on the latest trends and best practices to optimize your network visibility and analysis.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Security group.
Share your thoughts today