Extending Operational Intelligence for GigaSECURE with Gigamon Visibility App for Splunk
Updated October 28, 2021.
Next generation business infrastructures and their IT operations teams rely on a variety of tools to analyze wire and traffic data for security, application, and network performance monitoring.
But what is the glue that ties these tools together? How can the SecOps or NetOps teams gain full operational visibility?
Specialized solutions like Splunk, are deployed to gain operational intelligence, as well as to analyze and visualize actionable insights from all of this machine data.
Gigamon plays a key role in this ecosystem by facilitating the optimal delivery of traffic to the tools that generate logs and alerts to Splunk. At Gigamon, we have always had a singular focus on visibility – the type of pervasive visibility that uncovers blind spots to help detect threats in the infrastructure.
The formidable reach of our Unified Visibility Fabric™, that underpins our Security Delivery Platform, becomes even more compelling when one considers the vast ecosystem of technology partners that we work with to deliver accurate, intelligent access to network traffic and flow records in real time.
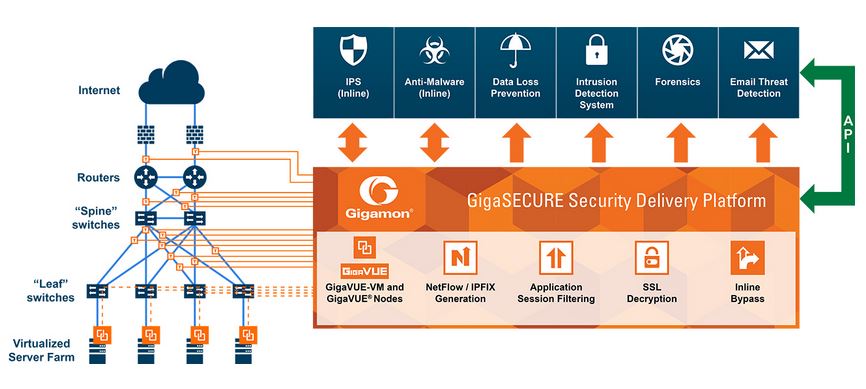
Visibility is undoubtedly the starting point to any threat detection and network protection. As shown in this diagram, the GigaSECURE® Security Delivery Platform is the foundation for the effective security architecture. Security tools can be deployed either inline or out-of-band and dynamically obtain access to just the traffic they need—physical and virtual—anywhere in the infrastructure.
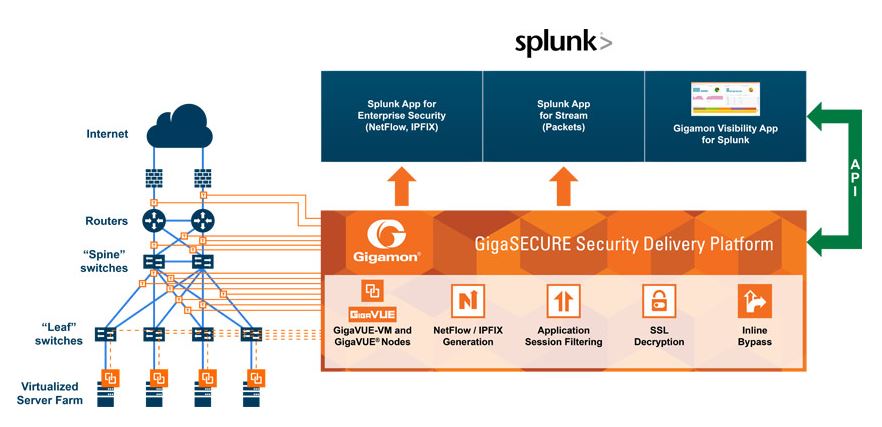
So how does Splunk integrate with GigaSECURE? Is the integration for traffic analytics, log analysis or both?
The Gigamon Visibility App for Splunk can be used to visualize the policies and sources of the traffic that trigger the KPIs and alerts within Splunk. This app reports on the health, inventory, and analytics of the GigaSECURE security delivery platform. These include: hardware health, port details, GigaSMART traffic policies, trends, top conversations, audit events, and syslog alerts.
GigaSECURE can be deployed to aggregate and isolate key traffic streams to feed packet data to the Splunk App for Stream or provide high-fidelity, un-sampled NetFlow or IPFIX records to Splunk App for Enterprise Security.
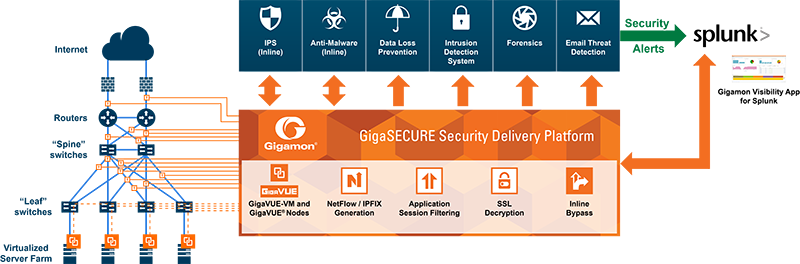
In best-of-breed security environments, which include Splunk, operators can also use third-party vendor tools to trigger security alerts based on KPIs or signatures.
With this multi-pronged integration of GigaSECURE with Splunk, the SecOps and NetOps teams can now gain network and security operational intelligence while visualizing the trends and patterns within the security delivery platform that signal bottlenecks and anomalies.
For more details about the app, refer to https://www.gigamon.com/products/technology/gigamon-visibility-app-splunk. You can also download the app from the Splunk Store.
To learn more, visit gigamon.com or access the free app via App Store on splunk.com.