How Multi-Cloud Visibility Ensures Business Continuity
Updated September 30, 2021.
Today’s powerful digital applications often span multiple tiers running on multiple on-premises and cloud platforms. This can lead to a fragmented, inconsistent view of data in motion and visibility gaps and blind spots that make it hard to deliver a secure, optimal user experience.
Gigamon Hawk closes the hybrid cloud visibility gap by providing IT with a single, consistent view into all data in motion from Layers 2–7 and East-West traffic across all platforms, including between clouds. This enables operations and security teams to ensure a positive, secure user experience and to optimize tools and traffic costs.
There are many ways that hybrid and multi-cloud visibility is beneficial – even critical – to ensuring application availability and business continuity. One of the most common applications and use cases that we’ve seen for this capability is tracking the status of SSL/TLS certificates on the thousands of application and communication servers that make up an enterprise network.
At a business level, if a TLS certificate expires it can take servers offline, leading to service outages, lost revenue opportunities, and reputational damage — which has happened in well-publicized incidents at organizations ranging from Adobe to Yahoo. At the IT level, dealing with these fire drills is highly disruptive to the flow of IT operations and is very inefficient.
Of course, tracking TLS certificates is a difficult process that is made even more resource- and time-consuming by the sheer volume of certificates and keys — often as many as 50,000 — that must be tracked. Because tracking expired, expiring, weak cipher, self-signed, or fraudulent certificates is so important and so resource-intensive, it is a natural candidate for automation. However, as the hybrid network becomes even more complex, so does automating this process.
Let’s take an example of an organization that has decided to create a TLS certificate traffic app on Splunk running on AWS. This app needs to get its tracking information from servers that could be in the public cloud, private cloud, and in multiple on-premises data centers. Ideally, this TLS tracking information should be sent as metadata to Splunk to minimize traffic flow and consumption-related costs.
While this process is easy to describe, it’s much more difficult to develop and implement. If you were to approach it from scratch, IT would need to build a pipeline that is able to log into each of the thousands of servers in the enterprise to check on the TLS certificate, and then report alerts of those that are about to expire, are self-signed, have weak ciphers, and so on. As a result, there are many TLS certificate management solutions available, but many of these are platform-specific, resulting in hybrid or multi-cloud enterprises running multiple certificate management solutions and not being able to easily gain a single view — or overall control — of their situation.
With Gigamon Hawk, this process can be radically simplified. The Gigamon fabric manager provides a single view into all of your hybrid platforms and is tightly integrated with cloud-native visibility tools, including AWS Traffic Mirroring, VMware ESX and NSX-T, Nutanix Flow and Prism, and OpenStack Tap as a Service. This means that Hawk has visibility into certificate status and can feed this into a tool like Splunk to automate the management process, saving significant amounts of the ops team’s time, heading off fire drills, and protecting the enterprise against outages.
As we mentioned earlier, if you want to deploy a TLS tracking app on Splunk, it’s much more efficient — and potentially less expensive — to send this data to Splunk as NetFlow metadata, not raw network packets. Gigamon can make SIEMs like Splunk much more powerful, efficient, and actionable by providing metadata collected from Layer 4 through Layer 7.
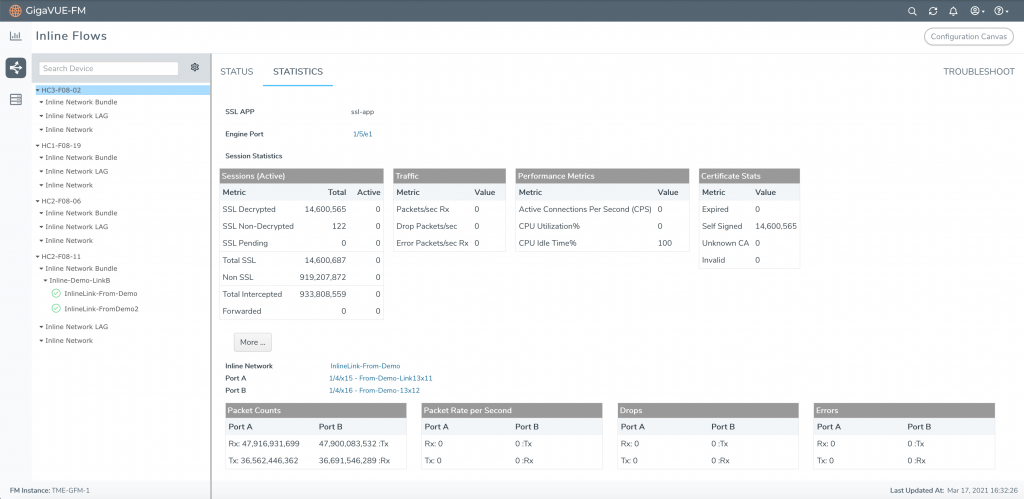
Using Gigamon Application Intelligence, we’re able to extract any of 5,000 application and network metadata attributes, including key attributes related to TLS certificates. By sending the right metadata information to our TLS Tracking app in Splunk, we’re able to quickly identify weak ciphers and expired or soon-to-expire certificates.
This is a very practical example of the benefits of using Gigamon Hawk and Gigamon Application Metadata Intelligence to automate and streamline a very resource-intensive process and one that, if not properly implemented, can have adverse effects on application availability and business continuity, and therefore on customer and user experience.
Want to Know More?
To see this process in action, please watch our video on multi-cloud visibility where we show how Gigamon Hawk tackles this use case.
Featured Webinars
Hear from our experts on the latest trends and best practices to optimize your network visibility and analysis.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Hybrid/Public Cloud group.
Share your thoughts today








