Network Traffic Visibility in Microsoft Azure
When we introduced the industry’s first network traffic visibility solution for public cloud infrastructure-as-a-service (IaaS) starting with Amazon Web Services last year, enterprises running workloads in the public cloud were excited by the possibility of obtaining identical visibility across their on-premises and cloud environments. This week at Microsoft Ignite, we are delighted to introduce our network traffic visibility solution for Microsoft Azure.
The benefit for enterprises adopting Azure? Security Operations Centers can protect data-in-motion entering, traversing or leaving Azure.
Azure has seen some stunning growth of late. With Azure as one of the goliaths in the cloud IaaS segment coupled with the dominance of Microsoft in enterprise on-premises deployments, it was not surprising that our customer base showed considerable eagerness to see us extend our visibility solution to Azure.
Network Visibility in the Cloud: Why Does It Matter?
To begin, any IaaS customer must recognize the shared responsibility model in a public cloud – see Figure 1. In an IaaS, the cloud provider is responsible for the “bottom” part of the stack – physical security, host infrastructure and network controls for multi-tenancy – while the cloud customer is responsible for implementing data governance, application and data security, application level controls, client and end-point protection. This is true of any IaaS.
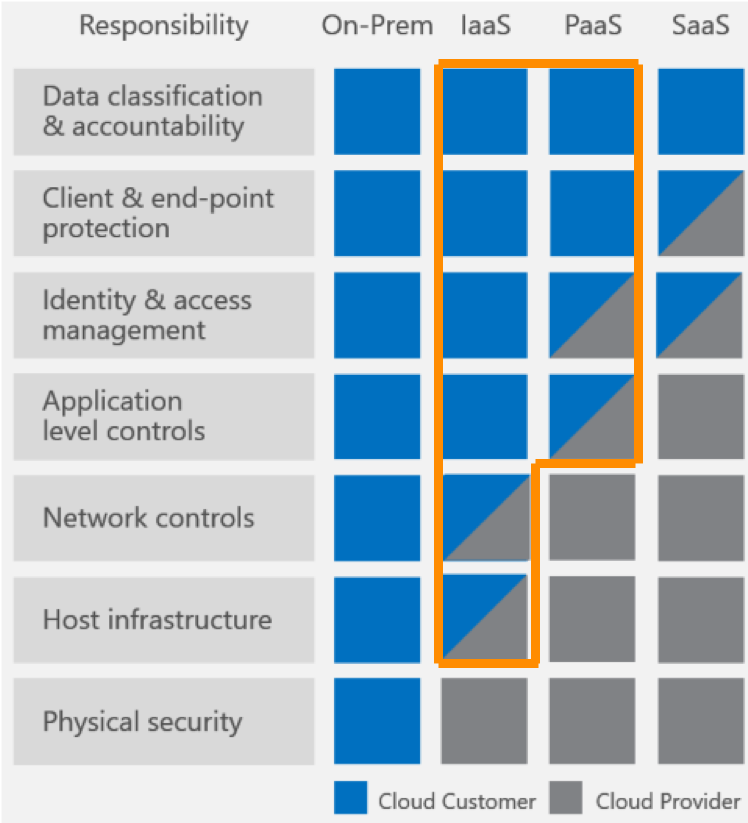
Figure 1: Shared Responsibility Model (source: Shared Responsibilities for Cloud Computing, Microsoft)
As cloud and information technology (IT) operational leaders evaluate IaaS to run mission-critical workloads in the cloud, data security, industry and organizational compliance, detection and response to anomalies become essential requirements. Security needs to extend beyond just identity and access management to encompass a full network security stack. In fact, a recent Vanson Bourne survey found that 90 percent of enterprises surveyed plan to approach cloud security in the same way they approach their on-premises security operations – with visibility into network traffic as a pre-requisite to implementing an effective network security strategy in the cloud.
The Azure Solution – Enabling Multi-Cloud
Our solution for Azure has identical capabilities to the Visibility Platform for AWS. As Figure 2 illustrates, the GigaVUE-FM Fabric Manager integrates with Azure Monitor and Azure APIs to detect changes to virtual machines and virtual networks in Azure. A lightweight agent installed in the virtual machine acquires traffic while the V Series virtual visibility nodes aggregate, select, optimize and distribute traffic to any tools that require this network data.
Our platform-centric approach to visibility offers customers an immense range of possibilities to build a highly agile, scalable, robust and cost-effective security strategy. Symmetric capabilities are available across multiple IaaS providers. Whether organizations wish to use AWS for some workloads and Azure for others or to run certain others in an OpenStack private cloud or continue to run others on a VMware ESX/VMware NSX/Cisco ACI infrastructure on-premises, they can still benefit from consistent visibility across all these diverse environments.
With a common Visibility Platform, they can centralize their tools in one location and apply the necessary traffic intelligence in the Visibility Platform to dynamically steer traffic of interest regardless of where the tools reside – in AWS, in Azure or even on-premises! In fact, traffic could also cross regions or virtual networks and virtual private clouds to enable security operations teams to implement centralized cloud and enterprise on-premises monitoring.
Interested in a Technology Preview or Beta?
We are currently in a technology preview of our Visibility Platform for Azure. Betas with customers will commence later this year. To learn more, please make use of one of the following options:
- Visit us at Microsoft Ignite in Orlando and speak to one of our subject matter experts September 25-27 at OCCC, West Building Level 2, 225B between 2:00 p.m. – 4:00 p.m.
- Attend the Microsoft Ignite breakout session BRK4032 “Monitoring, Diagnosing and Debugging with Azure Networking” on Friday, September 29, at 9 a.m. at the Hyatt Regency Windermere, where our Director of Product Management Sesh Sayani will join Microsoft to share more details.
- Email [email protected].
- Visit gigamon.com/azure.









