A Cloud Security Gamechanger from Gigamon and New Relic
I am an astronomy nut, and 80 years ago our universe changed — literally. The invention of the radio telescope opened a new perspective into how we’ve been observing the heavens for centuries. We can now examine the universe day or night, through bad weather, through atmospheric noise, and even through intergalactic haze.
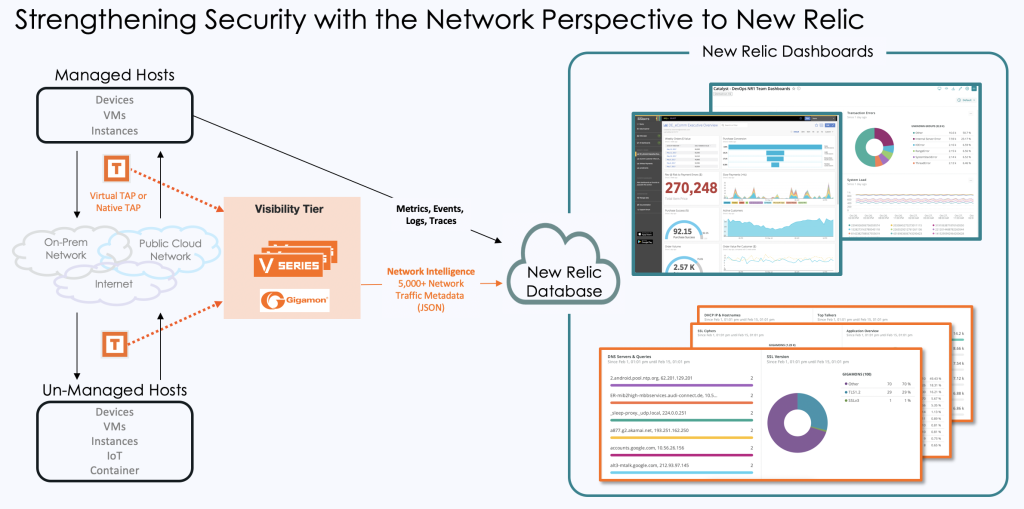
As radio waves expanded the spectrum of what’s observable, it’s not a stretch to say that the Gigamon New Relic quickstart is expanding metrics, events, logs, and traces (MELT) to a new universe of visibility using hybrid cloud network intelligence (HCNI). While there are many monitoring, migration, and troubleshooting use cases for HCNI, we are initially focusing on security, the most acute of cloud concerns and where the unknown unknowns matter the most.
Houston, We Have an Opportunity
Today’s cloud monitoring and security is sufficient, right? It may be for performance optimization, reliability engineering, and operational monitoring, but the answer is not so clear when it comes to a deeper level of troubleshooting, cost optimization, and security. Even with a full set of cloud service provider (CSP) and observability tools, it’s difficult or impossible to address challenges such as:
- Attaining complete visibility and eliminating blind spots, such as hybrid cloud application activities, container communications, and discovering and monitoring unmanaged hosts/apps and IoT
- Providing comprehensive security, such as detect and respond to network-based threats, enumerating hosts on the hybrid cloud network, and supporting shared responsibility and Zero Trust frameworks
- Detecting unwanted activities, such as shadow IT, crypto-mining, and P2P and torrent traffic
- Complying with network-related compliance and SLOs, such as extending on-premises policies, controls, reports, and practice knowledge to cloud apps
Network Traffic — the Ground Truth
As IT builds or migrates workloads to the cloud, we often hear, “We don’t have to do anything with the network — our CSP guarantees SLA for cloud infrastructure.” Despite SLAs, seasoned cloud adopters know there’s tremendous value in collecting and mining network data for many use cases.
That is where hybrid cloud network intelligence ups the game. HCNI telemetry is composed of packets, flows, and metadata, and is the “ground truth” of what’s being communicated and cannot be manipulated. While MELT information is critical in answering known unknowns, HCNI is foundational in answering the unknown unknowns.
In today’s universe of cloud tools, some:
- Ingest and process raw packets to detect intrusions and network threats, prevent data loss, and support data access governance requirements.
- Function using flow logs or NetFlow for use cases like DDoS, data exfiltration, and billing. By the way, here’s how Gigamon’s approach to flow records differs from AWS flow logs.
- And some consume application metadata far beyond NetFlow or AWS flow logs’ few attributes, to a much more extensive set of network intelligence data points. The Gigamon New Relic quickstart falls into this group.
Gigamon HCNI — How It Works and What It Offers
Using deep packet inspection, Gigamon Cloud Suite makes it possible to extract any combination of over 5,000 metadata attributes from hybrid cloud network traffic. App developers and operations and security teams can import the traffic metadata into their tools using IPFIX and CEF formats, and in the case of New Relic, JSON.
Four Gigamon elements work together for this New Relic integration:
- Traffic access. Gigamon can collect data from any source, using either native methods, like AWS VPC Traffic Mirroring, or a Gigamon virtual TAP for VM and container traffic.
For workload scaling up/down, Gigamon supports all native orchestration and automation choices, such as CloudFormation, Terraform, Puppet/Chef, Ansible, and SALT. - Traffic transformation. Gigamon Cloud Suite, also known as V Series, then aggregates and optimizes the traffic with functions such as packet de-duplication, packet slicing, PII (personally identifiable information) data masking, NetFlow record generation, and, of course, application metadata generation.
After optimization and transformation, you choose which metadata attributes to send to New Relic. Note to Gigamon customers: You will need to install a new metadata JSON conversion module in GigaVUE® V Series or GigaVUE HC Series. - New Relic Instant Observability quickstart. At this stage, you can point the radio telescope in any direction in the sky. We provide a few security samples in New Relic I/O, and we can explore additional use cases with you for your infrastructure.
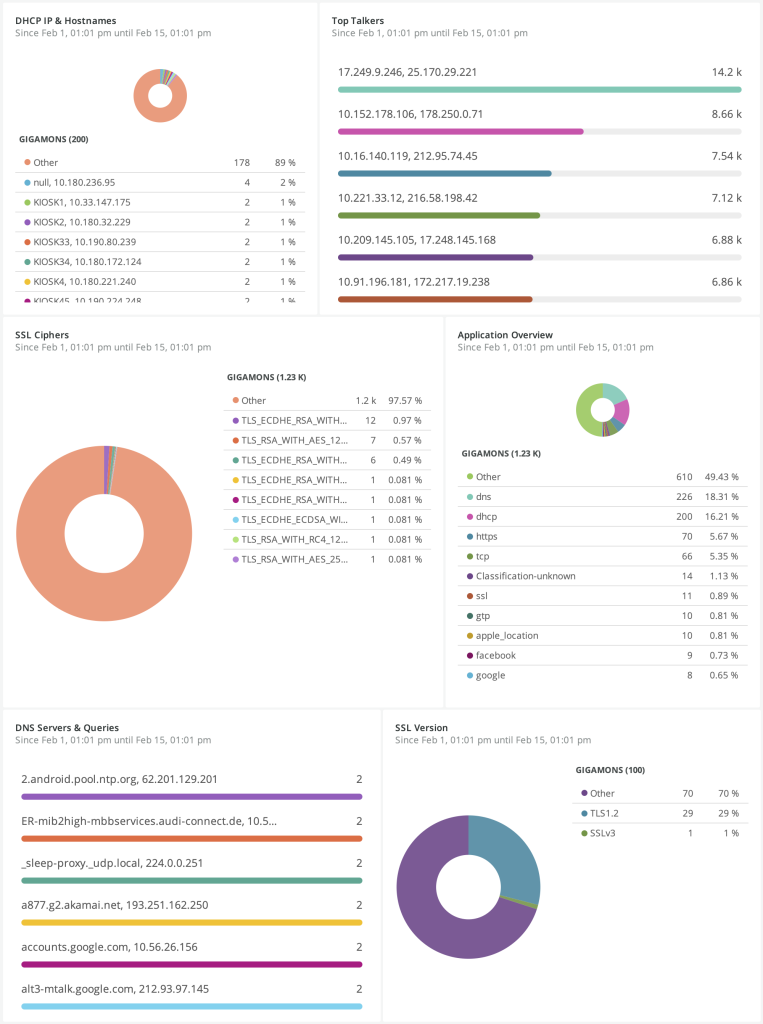
The Gigamon New Relic quickstart includes the ability to:
- Identify apps or hosts that are using weak ciphers for network compliance
- Identify expired or about-to-expire TLS certificates and detect traffic using non-trusted or self-certified certificates
- Discover rogue DNS/DHCP servers for shadow IT or nefarious purposes, such as man-in-the-middle diverting app traffic
- Identify data exfiltration by evaluating the frequency, volume, and type of DNS requests and tunneling activities
- Detect unauthorized external remote connections over protocols like SSH, Remote Desktop Protocol (RDP), and telnet
- Analyze HTTP client errors to track resource availability, find client-experience errors, or spot threat actors attempting brute force attacks with 401 error codes
- Analyze poor app response times by tracking the delta between DNS, TCP, and HTTP response times
A Quickstart to Long-Lasting Security
We are very excited about innovating with HCNI, bringing the network context to hybrid cloud monitoring. What is even more exciting for us is how New Relic makes this power readily available to InfoSec, operations, and developers.
To get more information, read our Gigamon–New Relic joint solution brief. And to see the Gigamon New Relic quickstart in action, request a demo from a Gigamon cloud expert.
Featured Webinars
Hear from our experts on the latest trends and best practices to optimize your network visibility and analysis.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Hybrid/Public Cloud group.
Share your thoughts today