GigaVUE-OS 5.7 Is Now Available with Application Metadata Intelligence — and a Lot More
Updated October 28, 2021.
With these dog days of summer comes the release of our latest GigaVUE-OS and GigaVUE-FM software, as well as our new enterprise license platform. Read on for how this release will help accelerate your digital transformation journey by meeting your immediate networking, security, cloud and scalability requirements in the world of increasingly distributed applications.
Here are some highlights:
- Identify more than 5,000 application metadata attributes related to security, network performance and user experience with the new Application Metadata Intelligence GigaSMART® application
- Float application licenses between GigaSMART cards and easily see and manage all of your purchased software
- Gain visibility into any cloud environment, public or private, using our new Any Cloud framework
- Obtain visibility into container (Kubernetes/Docker) traffic using agentless monitoring for aggregation, filtering and distribution to network and security tools
- Improve security using role-based access control management and automate routine tasks with Ansible integration
- Enable tools to conduct accurate and reliable network and application performance monitoring with Time Stamping on GigaVUE-TA200
- Simplify your inline SSL policy definition and management using the graphical drag-and-drop feature with Flex Inline SSL Decryption
Below, you’ll find more detailed information on these capabilities.
#1. Application Metadata Intelligence, a New GigaSMART Application Available as a Subscription Service
More and more organizations are adopting digital applications, with IDC predicting1 that the digital transformation market will reach $1.97T in 2022. But operations can find it overwhelming to digest and prioritize all the data in motion (including digital apps) from their infrastructure being sent to their analytic tools, such as SIEMs.
With that in mind, we’re excited to announce Gigamon Application Metadata Intelligence, a new GigaSMART application that uses deep packet inspection to extract more than 5,000 application metadata attributes related to security, network and application performance, and user experience.
This new feature extends Gigamon metadata generation and forwarding technology to applications and protocols (Layer 7). With it you can optimize tool use (such as SIEMs) by exporting only contextual metadata instead of raw network packets.
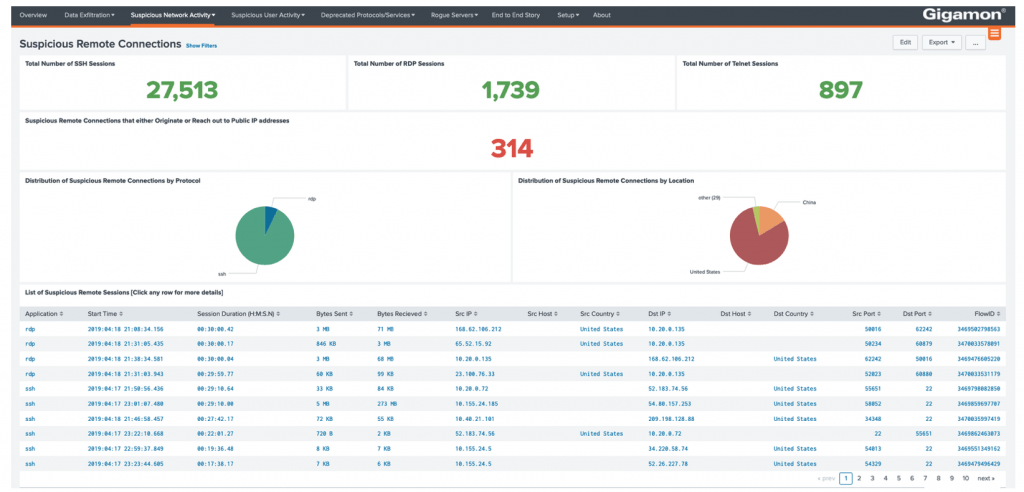
As seen in Figure 1 above, the Application Metadata subscription service enables you to:
- Visualize and measure performance, troubleshoot, spot events and improve tool effectiveness
- Increase network performance and uptime by learning details behind bottlenecks and outages
- Support forensic investigators hunting threats and breaches from shadow IT and file sharing sites
- Secure communication by using Layer 7 metadata to prevent malicious commands
- Optimize multiple tools — including SIEMs and network and performance monitoring tools — by exporting only contextual metadata
- Ensure security by blocking select social media users, SQL queries and requested files or videos
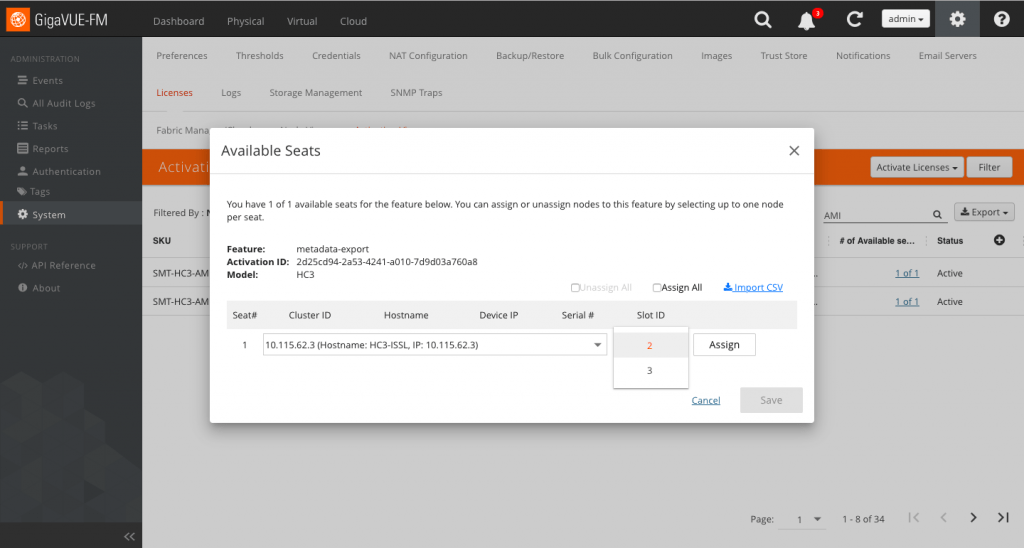
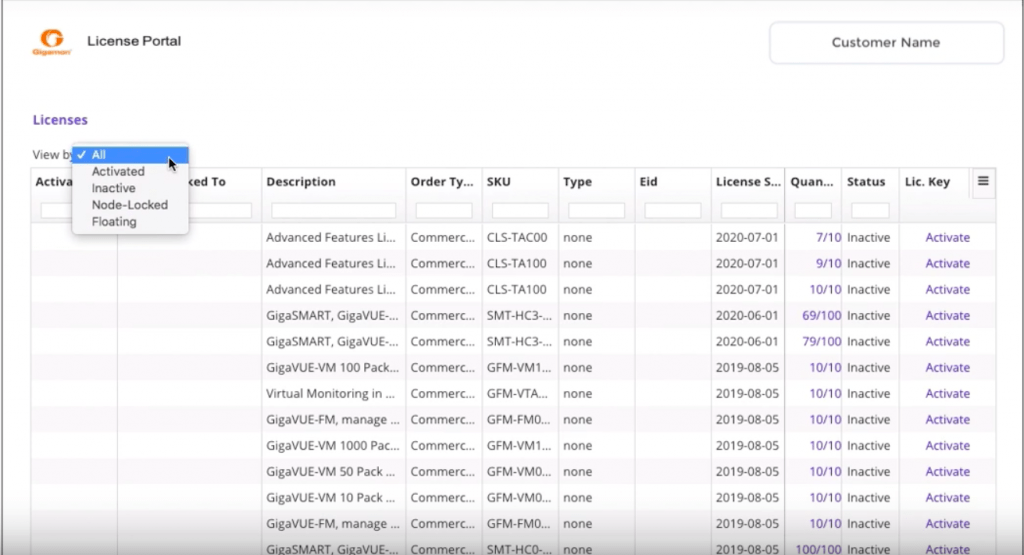
#2. Enterprise License Platform to Easily Purchase, Activate, Track and Manage GigaSMART Application Licenses
If you want to float GigaSMART application licenses between GigaSMART cards within similar types of GigaVUE-HC series nodes, then this is the perfect time to leverage our new enterprise license platform, which includes GigaVUE-FM 5.7 and the Gigamon License Portal, as shown in Figures 2 and 3.
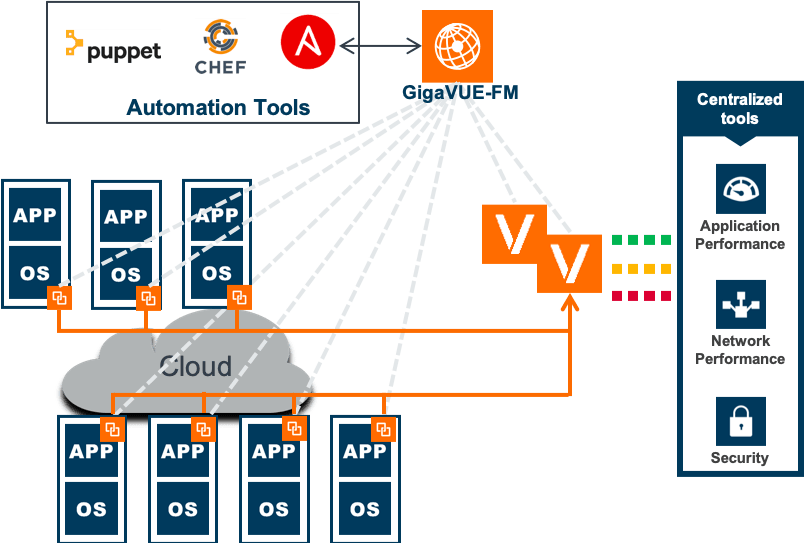
#3. Visibility into Any Cloud Environment (Public or Private) Using a Cloud-Agnostic Deployment
As shown in Figure 4, with the new agent-based Any Cloud architecture you can gain visibility into any cloud environment with GigaVUE-FM 5.7:
- Cloud agnostic: Google Cloud, Nutanix, Azure Stack, Hyper-V
- Deploy agent-based G-vTAP and V-Series nodes through automation tools like Ansible, Puppet, Chef and Terraform
- Discover G-vTAPs and workloads, using GigaVUE V Series nodes and implement alerting through GigaVUE-FM 5.7
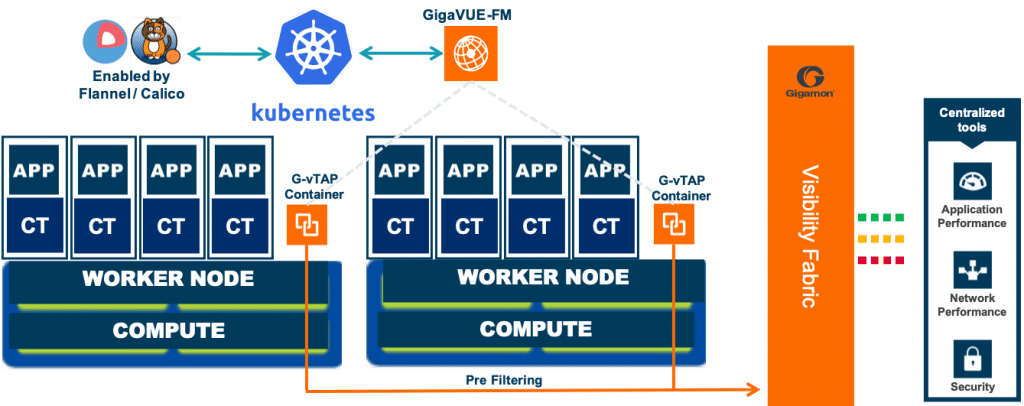
#4. Visibility into Containers Using Agentless Monitoring
Until now, you didn’t have a Gigamon solution providing visibility into containers. As shown in Figure 5, with this new release you can gain visibility into container (Kubernetes/Docker) traffic.
Other new features include:
- Agentless monitoring with G-vTAP containers
- GigaVUE-FM provides orchestration from Kubernetes master
- Support network overlays: Calico and Flannel
- Tunnels traffic to physical or virtual visibility nodes
- Supports multi-cloud scenarios with native Kubernetes controller
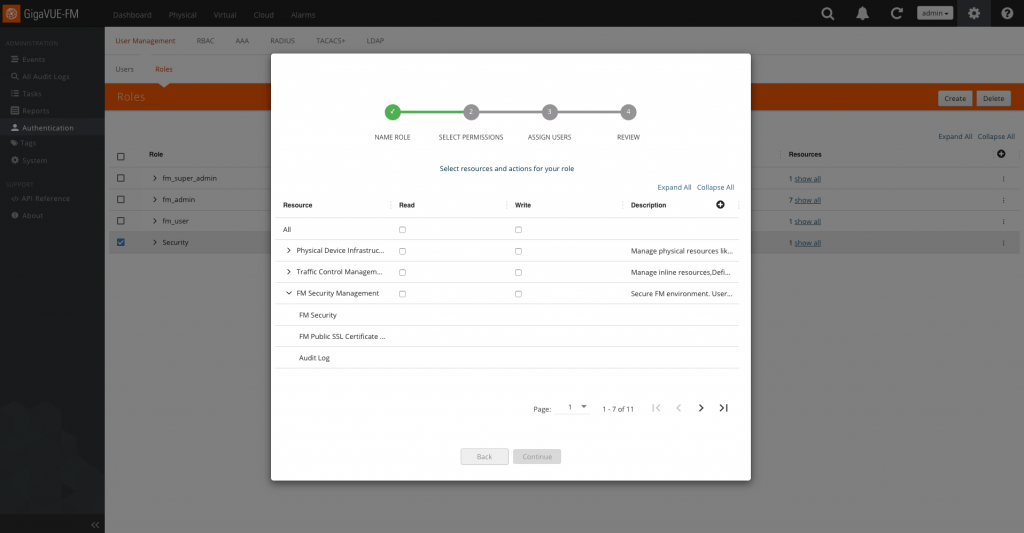
#5. Improved Security, Management and Automation Through GigaVUE-FM
As shown in Figure 6, with this new release of GigaVUE-FM you can now use role-based access control (RBAC) to:
- Create custom roles for different types of operators
- Assign granular Gigamon fabric resources for different roles
- Prevent unauthorized changes
- Decrease risk of breaches and data leakage
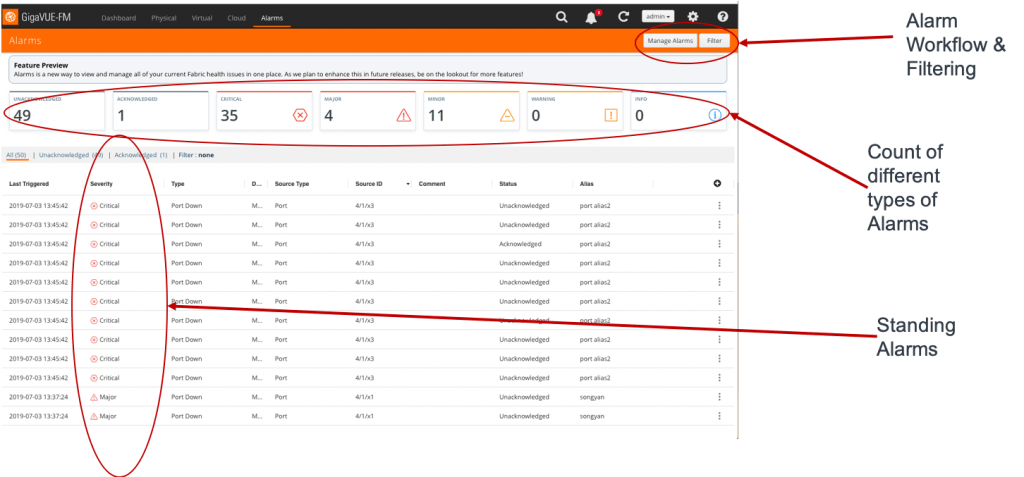
Alarm Management
This release of GigaVUE-FM also features Alarm Management, which, as shown in Figure 7, lets you:
- Identify and consolidate all Visibility Fabric™ faults in a single console
- Provide basic alarm-management workflows for a team of operators
- Identify root causes by co-relating alarms across different objects
- Reduce mean time to repair (MTTR) of faults
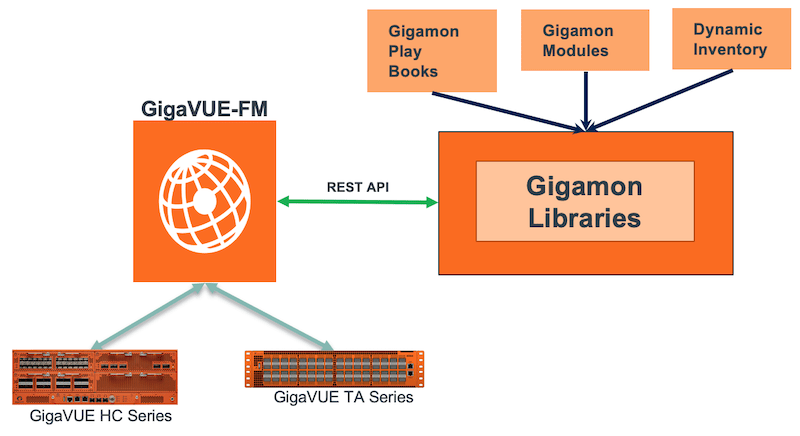
GigaVUE-FM Automation with Ansible
Previously, you had to manually perform routine tasks such as configuring the Visibility Fabric or making bulk changes to Gigamon visibility nodes. Our new GigaVUE-FM integration with Ansible provides Ansible playbooks, modules and libraries that automate repeatable Visibility Fabric management tasks and bulk configurations, such as:
- Device commissioning
- Traffic provisioning
- Infrastructure commissioning
- Automated playbook generation
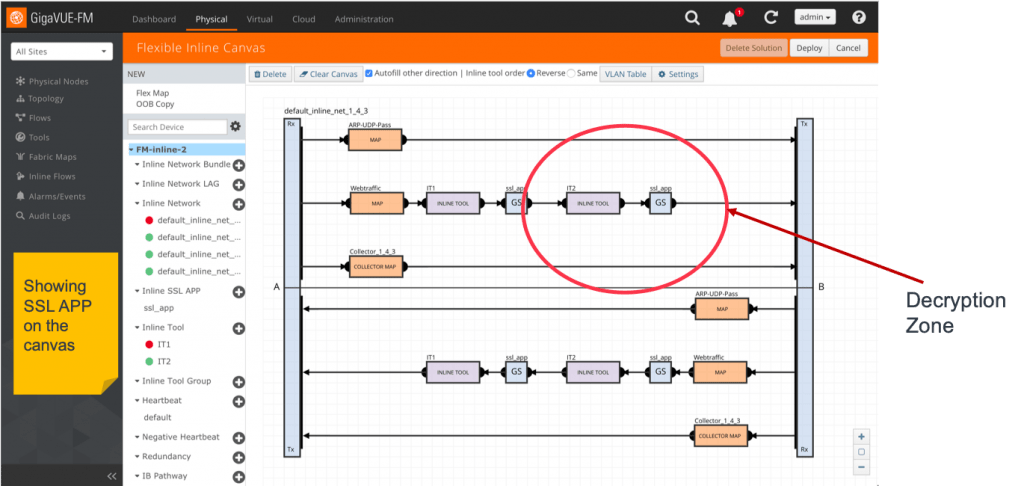
#6. Simplified Inline SSL Policy Definition and Management Using Flex Inline SSL
Until now it was cumbersome to configure inline SSL decryption and difficult to understand. As shown in Figure 9, you can now use the drag-and-drop GUI feature in GigaVUE-FM to easily configure and visualize SSL policy definition and management.
Learn More
Check out these resources to learn more about Application Metadata Intelligence, GigaVUE-FM and other GigaVUE-OS enhancements:
- Gigamon Application Metadata
- GigaVUE-FM series data sheet
- GigaVUE® Cloud Suite for Containers (Kubernetes/Docker) solution brief
- Video: New enterprise license platform
Featured Webinars
Hear from our experts on the latest trends and best practices to optimize your network visibility and analysis.

CONTINUE THE DISCUSSION
People are talking about this in the Gigamon Community’s Networking group.
Share your thoughts today
1. IDC. “Worldwide Spending on Digital Transformation Will Be Nearly $2 Trillion in 2022 as Organizations Commit to DX, According to a New IDC Spending Guide.” IDC, November 13, 2018. https://www.idc.com/getdoc.jsp?containerId=prUS44440318.








 Sam Kumarsamy
Sam Kumarsamy