Four-Starstruck: On Meeting General Michael Hayden
“How’s Mulder? Tell him I say hi.”
It’s the perennial question and request from one of my good friends when he’s checking in on my dad. He thinks he’s amusing. (Admittedly, I do, too.)
After serving 20 years in the military, my dad worked for another 20 at the NSA. To this day, I still can’t tell you what he did—though that may be less to do with national security and more with the fact that my brain is a sieve. Heck, to remember his first NSA assignment in 1989, I had to write it down: The Office of the Assistant Secretary of Defense for Command and Control Communications and Intelligence at the Pentagon. The nomenclature for governmental departments is about as unambiguous—and yet confusing—as the German language.
But back to (or on to, as the case may be) my point. I’m an ex-Army brat who moved around a lot while growing up and who, in a different way, was moved while on a team teleconference to discuss Gigamon’s inaugural “We Fight Smart Federal Cyber Security Summit” in DC. One of my colleagues announced that we’d secured General Michael Hayden—former head of the NSA and the CIA—as the keynote speaker. I looked across my desk to the book my father had just gifted me: Playing to the Edge: American Intelligence in the Age of Terror by General Michael Hayden. The one in which he’d also penciled in checkmarks in the table of contents next to the chapters that correlated to his time at the agency.
Like an unconscious reflex, I raised my virtual hand (meaning I sent an email): “Hayden? Did you just say General Hayden? What can I do to go?!” [An aside: I’m a near-agoraphobic homebody who never volunteers to travel.]
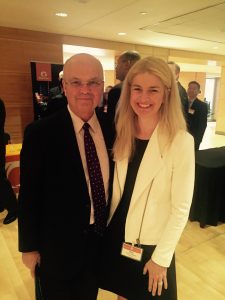
Between that call and now, I’ve finished the book, attended the summit, and met the good General Hayden.
Today’s Top Cyber Sins and Sinners
At a high level, Hayden categorized cyber sins:
1. Stealing your stuff
2. Corrupting your stuff
3. Denying you access to your stuff (e.g., Think ransomware)
4. Creating physical destruction
And sinners:
1. Nation states
2. Criminal gangs
3. Hacktivists
While “stuff stealing” has been a fundamental cyber sin, it’s begun to bleed down the rest of the list. As examples, Hayden mentioned the recent hack on the Ukrainian power grid; the Stuxnet attack, which he dubbed the poster child for how someone used a weapon composed of ones and zeroes to destroy a thousand nuclear centrifuges; and the Sony North America breach, an atypical but nation-state-directed attack nonetheless.
See, nation states generally attack other nation states—not corporations like Sony. But Sony mocked Kim Jong-un in a silly movie; Kim Jong-un got his revenge; and now Sony is probably much more reluctant to do anything to insult North Korea as a result of the cyber sin palooza it endured and which included data theft, data wiping, data access denial, and emotional impact (meaning employees received disturbing messages regarding their personal information along the lines of “I know where you live, I know what kind of car you drive.”) Yuck.
Each of these attacks shows the progression down the cyber sin list to more and more destructive activities and verifies that attacks on the cyber domain can affect more than the cyber domain. They can touch any and all of the other four warfare domains of land, air, sea, and space.
By contrast, and in a category all its own, there is legitimate state espionage. Like that of the OPM hack.
“This is not shame on China. This is shame on us,” said Hayden. “If I could have done this against the comparable Chinese database, I would have done it in a heartbeat.”
To be clear, he wasn’t saying it was a good thing; only that it was not illegitimate. The U.S. steals data, too—but with the caveat that it is doing so for the sake of freedom and safety and not, as so many other nation states do, for economic advantage. Hayden named the Iranians, Chinese, North Koreans, and Russians as prominent actors, adding that the Chinese have scale (breadth, depth, persistence) while the Russians have superb skill.
Make Room for the Private Sector
As opposed to during business meetings a few years back, Hayden said that executives today are no longer asking how much cyber security is going to cost them, as if it were something that would subtract from the bottom line. Instead, industry knows that cyber security isn’t a bottom line issue and that, without it, there is no top line.
He also highlighted the importance of the private sector for the development and advancement of cyber security.
“There is incredible entrepreneurial and technological energy in the private sector to provide security in the cyber domain that we have been accustomed to the government providing in the other domains,” he said. “The private sector is going to be responsible for your safety in the cyber domain in a way you have not been required to be responsible for your safety down here [in the areas of land, sea, air, and space] since the closing of the American frontier in 1890.”
Risk = Threat x Vulnerability x Consequence
Hayden took us through this equation. In it, he said, if you can get any factor down to zero (or close to it), you win.
Historically, cyber security has been about reducing the “v” (vulnerability) factor by defending at the perimeter and reducing attack surfaces. But even if you do “v” perfectly, you might keep 80 percent of the less talented attackers out of your network, but the other 20 percent will still get in. So keep defending at the perimeter to eliminate low-level threats, but know that it’s not sufficient and that you won’t win at the edge.
Instead, and with the increasing number of attack surfaces, the more current technological effort—and where Gigamon fits into the equation—is with “c” (consequence management). It is presumption of a breach, survival under attack, and putting the most effort into securing your most valuable assets. It’s about defense in depth, self-awareness, resilience, and recovery. Finding and responding in real-time to network anomalies.
Per Hayden, “The difference between an A and F player is not penetration. The difference is between flash and bang. The difference is between penetration and discovery of penetration.”
And “t” (threat)? In the cyber domain, “t” is tough. In other domains, you can hit back. But attempting to conduct cyber counter battery fire, as Hayden called it, is not the best idea—and actually illegal if conducted from U.S. soil. The better focus, again, is on cyber threat intelligence.
Thank You, General Hayden
General Hayden concluded his presentation in saying, “We need to be careful how we defend in the cyber domain so that we don’t detract from its magnificence. Cyber security is not only about defense, but preserving why we did this thing in the first place.” Amen.
This weekend, we celebrated Memorial Day in the U.S., a holiday inaugurated after the Civil War to commemorate the fallen. At Gettysburg, Lincoln honored those who gave “the last full measure of devotion” in sacrificing their lives for the liberty of others. For me, the sentiment reaches to include those who’ve dedicated a lifetime of service to ensure the safety and freedom of their countrymen. If I had a chance to meet Hayden again (and actually utter a lucid line), I’d say thank you for your time, your support, and your service. I am grateful.
Please find the recording of his keynote here.